What Is Patch Tuesday and Why Should You Care?
You already know about Black Friday and Cyber Monday. But Patch Tuesday is more significant for the tech community,…
The 12 Benefits of Document Management Systems for Financial Institutions
With the exception of cybersecurity, the single best tech investment most financial institutions should make is a d…
What Is an Incident Response Plan and What Should Be in It?
An Incident Response Plan (IRP) should contain everything your organization will do in the event of a security inci…
What Is a Cybersecurity Assessment, and Do You Need One?
Business technology evolves from year to year. But cybersecurity can change by the month, and sometimes, by the day…
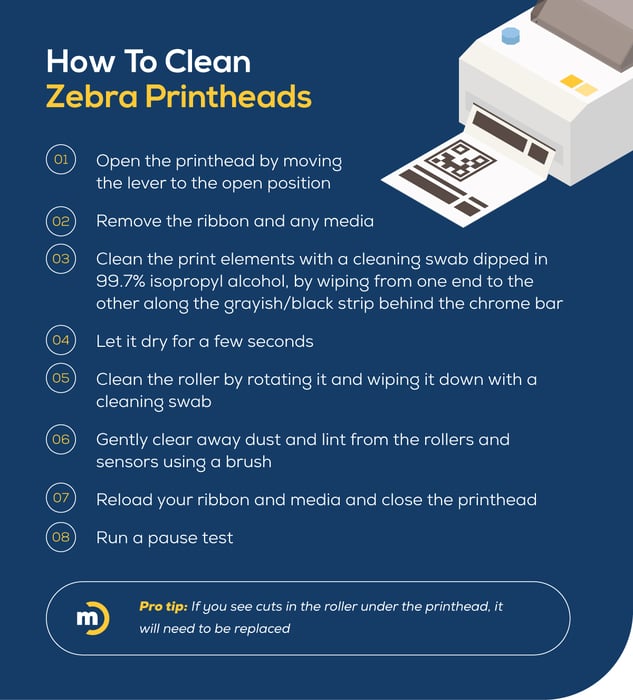
Your Guide to Zebra Printer Troubleshooting
Zebra printers have a solid reputation for reliability even in harsh conditions. But even printers known for their …
Mastering Cybersecurity Compliance in Regulated Industries
First off, I just want to say that I’ve never met a business owner who was happy about having to comply with regula…
What a Managed Print Services Provider Can Bring To Your Law Firm
It’s hard to overestimate the importance of having a reliable, secure print environment at a law firm. Any disrupti…
Everything You Need To Know About Cloud-Based Business Phones
It would be difficult to find an office where employees were still working on computers that couldn't connect to th…
The IT Leader's Guide to Achieving More ROI on Cisco Licenses
Most people would assume that you always get a better deal when you purchase something directly, as opposed to goin…