Top Cybersecurity Laws and Regulations To Know About in 2026
Many companies are now facing the challenges posed by malicious hackers attacking their IT environment. Unfortunate…
Email Security Best Practices: Essentials Every Business Should Use
Even though email security concerns are now taking center stage in many companies, let’s be honest — email was neve…
Financial Services Cybersecurity: Best Practices That Actually Hold Up
The financial services organizations that handle cybersecurity well aren't necessarily spending more than their pee…
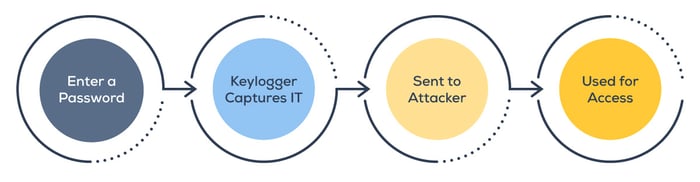
What Is a Keylogger and How Can You Protect Yourself?
You probably don't think much about what happens between the moment your fingers hit the keys and the moment your p…
What Long-Term Care Facilities Should Know About the Independent Living Systems Data Breach
Long-term care has quietly become one of the most targeted sectors in cybersecurity. In the first quarter of 2025 a…
What To Look for in a Small Business Cybersecurity Partner
There are two questions to ask a provider that often clear things up right away. First off, if they haven’t signifi…
Cybersecurity Compliance Requirements for Financial Services: A Simplified Checklist
If you're reading this, you're probably already drowning in compliance requirements. Maybe you're trying to figure …
5 Common Healthcare Cybersecurity Challenges (and How MDR/SOC Can Help)
In our conversations with healthcare clients, we hear the same five security challenges come up again and again. If…
What the St. Paul Cyberattack Means for Local Government Cybersecurity Throughout the US
The recent ransomware attack on the City of St. Paul should be a wake-up call for municipal governments nationwide.…