The Data Governance Institute defines data governance as “a system of decision rights and accountabilities for information-related processes, executed according to agreed-upon models which describe who can take what actions with what information, and when, under what circumstances, using what methods.” But that’s a bit of a mouthful, and information security isn’t everyone’s passion!
In this blog, I’d like to break down this concept a bit and talk about key takeaways for organizations that want to work smarter, reduce costs, and safeguard sensitive information.
So…What Is Data Governance?

Data governance sounds like just a bunch of rules, but it’s more than that. It’s about having a suite of tools and processes to help your business do more than you ever thought possible by protecting and harnessing the full power of the information you already have.
But protecting data isn’t just about tools and systems. It’s also about how your staff uses those tools and systems. So proper data governance should also include security awareness training for end users. Believe it or not, the biggest cybersecurity threat for most organizations is the actions of their own employees. But proper security awareness training can go a long way towards transforming your staff from the weakest point in your defenses to what we often describe in our industry as a “human firewall.”
Why Does Data Governance Matter?
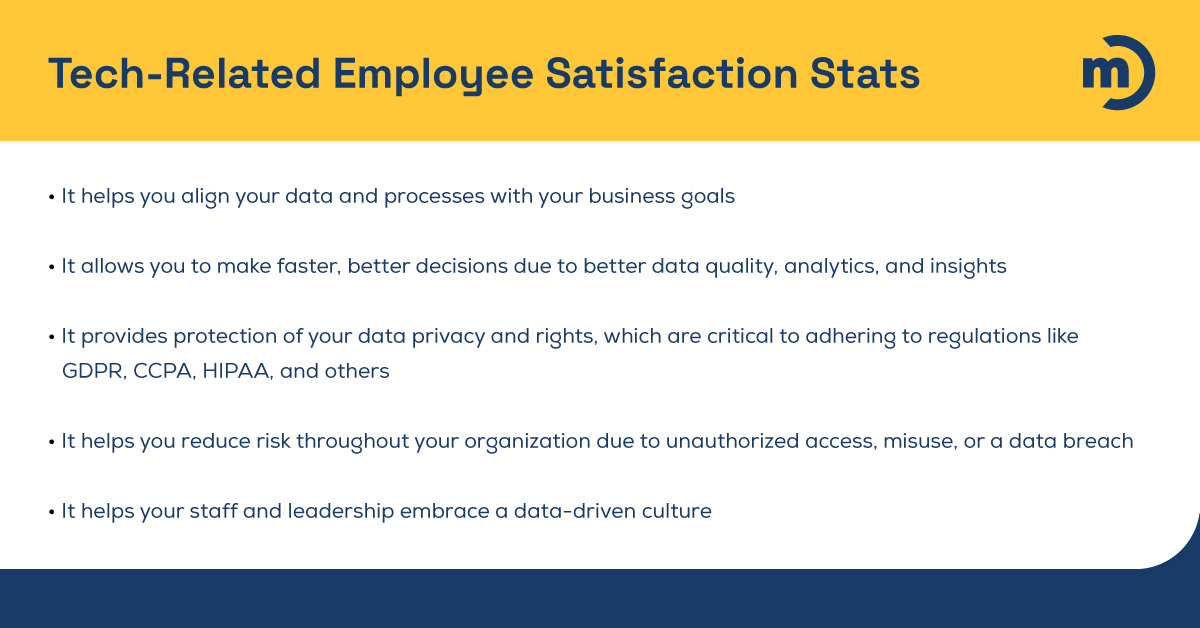
Data governance isn’t just about preventing bad things from happening! There are plenty of reasons that executives who want to help their company become more competitive should be interested in this topic — and a few other IT-related topics, for that matter.
One subject we’re passionate about at Marco is encouraging business leaders to understand what a phenomenal asset their internal IT teams can be. If you haven’t yet, ask your top tech talent about how you can achieve more results while reducing costs, and I’m guessing some of what they’ll talk to you about immediately falls under the banner of proper data governance.
If you doubt me, look over the following infographic.
Real-World Data Governance Examples
Data governance is a broad term, and it can bring different rewards to different organizations. It also isn’t just a one-time thing. When done correctly, it’s an ongoing program that should grow and change along with the organization it serves. But let’s get out of vague descriptions and into a few hypothetical scenarios to outline how proper data governance can help different businesses thrive.
“Saving the Restaurant Chain”
Let’s say you have a successful restaurant chain, and lately, you’ve been noticing that although your restaurants remain popular, your profits are down. Fortunately, you have some interesting data at your fingertips that suggests that the amount of wine and alcohol you purchase is no longer lining up with customer orders.
After a brief check-in with management, you know that your staff is behaving ethically, but you do need to implement a system for regulating pours. You’re able to make this change quickly and easily to restore profitability. And you aren’t tempted to make any misguided changes that could hurt your business in the long run, like cutting back on service or food quality.
“Avoiding an M&A Catastrophe”
Information silos are a common problem, and it’s notoriously difficult for, for example, software developers and marketers to speak the same language so they can collaborate well. The result of information silos within companies is frequently a huge waste of time and money and a lot of unnecessary frustration. But data silos are a frequently overlooked reason that otherwise sound mergers and acquisitions can fail.
So let’s say your company wants to add a new product, and the best way to do that is to acquire a smaller company that’s already producing a similar product and has the capabilities and the knowledge you need. They even have a wealth of information about who buys their product and why, and their customers’ purchase history. Everything about this deal looks amazing on paper, but this smaller company uses an entirely different tech stack and set of processes.
But that’s a small detail to sort out eventually, right? Wrong!
You know better and put on the brakes. Like Laurin Parthemos at Kotter said recently when asked about M&As, “If it’s not viable to integrate quickly, it’s likely not worth the purchase in the current economic environment.” Your company ends up finding another company that ends up being a better fit, and you are mindful of merging their processes with yours quickly. Their staff ends up being a powerhouse of information about how to delight their current customers, and you retain the full value of your transaction…and then some!
“Risk Reduction at Its Finest”
If you’re in IT, you already know this and probably have been saying it for years. But it’s hard for non-IT folks to understand why the best cybersecurity tools in the world can’t always protect them from the biggest cybersecurity threat there is — human error. The typical hacker isn’t some cybersecurity mastermind. They often have more in common with petty thieves in that they prefer to find easy opportunities to make a quick buck.
So let’s say that the healthcare organization you just joined is very proud to tell you that they’ve invested in the very best cybersecurity tools on the market to safeguard your data, systems, and tools. So your job, part of which involves making sure they’re in compliance with HIPAA, should be easy. But you read this blog, so you know that employees are typically an organization’s greatest cybersecurity threat. You ask them about their security awareness training program, and they stare back at you with blank faces.
You tell them what it is and why it’s important, and days later, they get the unpleasant news that thousands of patient records were released on the dark web after a few employees fell prey to a phishing scam. They will face some stiff fines, and rightly so, for failing to protect their data. But you know how to help them do better in the future. In the next ten years you’re with the company, it doesn’t happen again.
10 Data Governance Best Practices
Sometimes prevention is a hard sell; after all, it’s hard to quantify a thing that doesn’t happen. But the great thing about data governance is that it doesn’t just stop bad things from happening.
There are plenty of ways to sell data governance best practices to leadership. But there are a lot of them, so I’ll list them out in this blog and wrap things up with how to make them easier to implement.
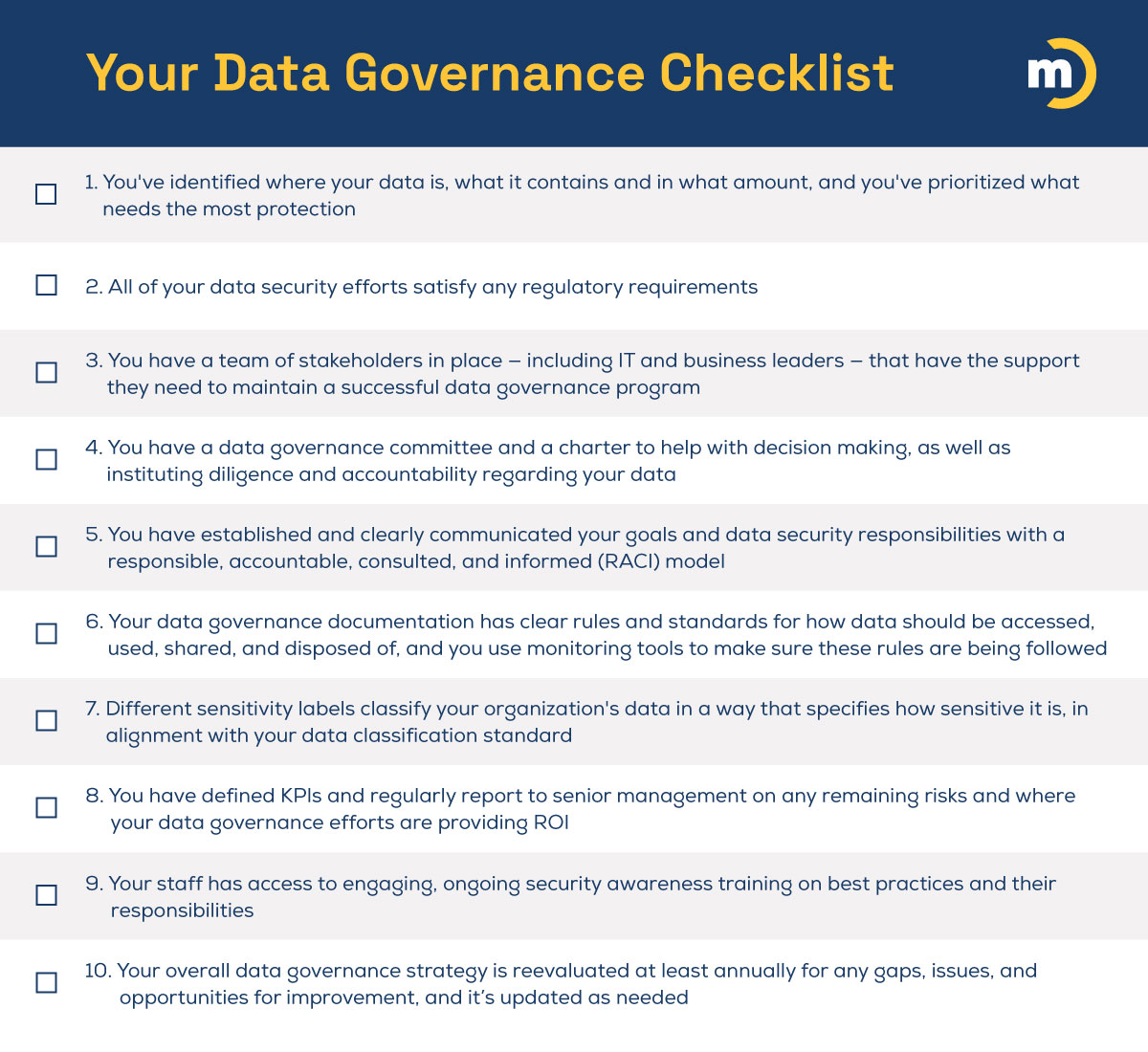
Are you currently following data governance best practices? Here’s a handy checklist to help you know where you’re following best practices and where you might need to make a few improvements.
How To Make a Data Protection Strategy Shortcut
If you remember nothing else from this blog, here are what I think are the most important takeaways: 1) A robust data security program can help you achieve a lot of big-picture goals, like reducing risk, improving efficiency, and boosting profits, and 2) Data governance goes beyond setting rules in place, as it involves collaborative decision-making to align with your business objectives.
But right now, some of you are probably thinking, “That’s all well and good, but it sounds like a lot of work we don’t have time for right now,” I get it. Businesses have had a rough few years, and many organizations are struggling to maintain the IT talent they need just to keep the lights on, let alone tackle the bigger stuff. Marco does offer thorough technology assessments, and if the previous sentence describes your organization, that’s what I’d recommend.
Click the button below to read more about our cybersecurity assessments and why they’ve been so popular with our clients!

