Top Cybersecurity Laws and Regulations To Know About in 2026
Many companies are now facing the challenges posed by malicious hackers attacking their IT environment. Unfortunate…
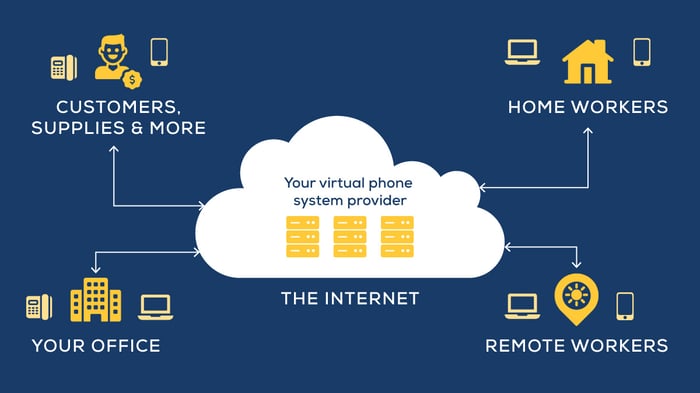
What’s Hosted Voice, and Why Should Your Business Use It?
If you’ve been researching ways to upgrade your business phone system and potentially save money, you probably have…
Email Security Best Practices: Essentials Every Business Should Use
Even though email security concerns are now taking center stage in many companies, let’s be honest — email was neve…
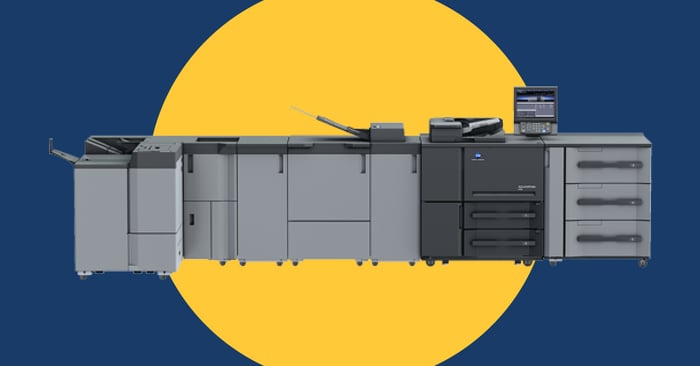
Questions To Ask Before Purchasing a Production Printer
Does your organization need to produce a lot of printed materials? If you do a significant amount of print marketin…
Financial Services Cybersecurity: Best Practices That Actually Hold Up
The financial services organizations that handle cybersecurity well aren't necessarily spending more than their pee…
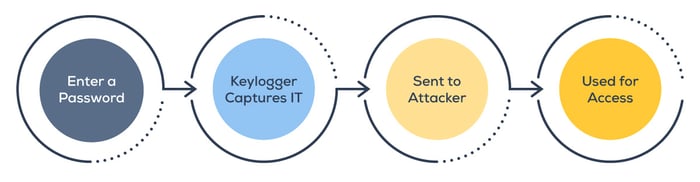
What Is a Keylogger and How Can You Protect Yourself?
You probably don't think much about what happens between the moment your fingers hit the keys and the moment your p…
How To Protect Your Business From Physical Security Risks
Over the last five years, 60% of companies have experienced some form of physical security breach. And in most of t…
Microsoft 365 E7: What the New Frontier Suite Means for Businesses
Microsoft made waves on March 9, 2026, when it announced the launch of Microsoft 365 E7 — a new licensing suite the…
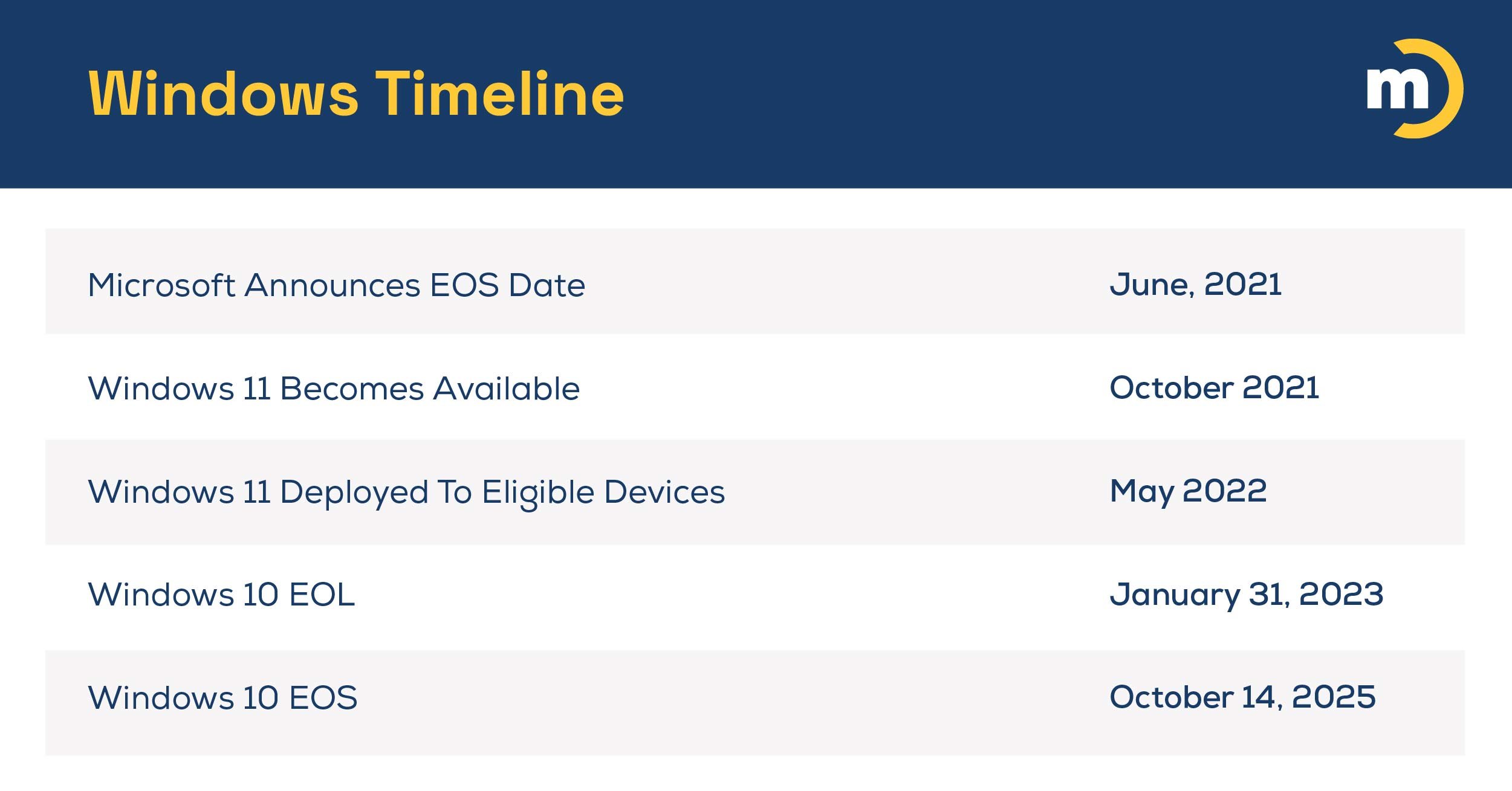
What Mitel’s MiVoice Business 10.5 “Final Release” Means for Businesses
If you’re running Mitel MiVoice Business on an AX, CX II/CXi II, or MXe III/MXe III-L controller, you may have hear…