What Mitel’s MiVoice Business 10.5 “Final Release” Means for Businesses
If you’re running Mitel MiVoice Business on an AX, CX II/CXi II, or MXe III/MXe III-L controller, you may have hear…
What Long-Term Care Facilities Should Know About the Independent Living Systems Data Breach
Long-term care has quietly become one of the most targeted sectors in cybersecurity. In the first quarter of 2025 a…
Microsoft Copilot Chat vs. Full Copilot: How To Decide What To Enable
Microsoft Copilot is no longer a future consideration for Microsoft 365 environments — it’s already here. Copilot C…
How M-Files and Microsoft Make Content AI-Ready
Many organizations have spent years investing in the Microsoft ecosystem — Microsoft 365, SharePoint, Teams, and no…
What To Look for in a Small Business Cybersecurity Partner
There are two questions to ask a provider that often clear things up right away. First off, if they haven’t signifi…
When Is Managed IT the Right Fit for Your Business?
Organizations have three options when it comes to managing their technology. They can handle all of their IT needs …
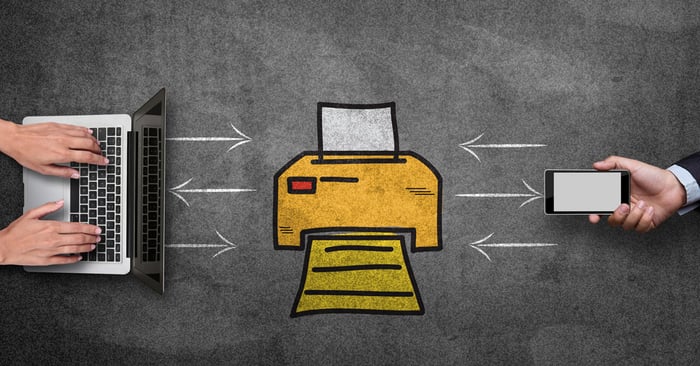
Local vs. Network Printers: Which Is Right for Your Business?
Printing may not be the flashiest part of your IT environment, but it plays a critical role in day-to-day business …
How Print Costs Impact Law Firm Profitability
At most businesses, unmanaged print costs amount to 1–3% of an organization’s total revenue. But if your print cost…
Microsoft 365 Pricing Changes in 2026
Microsoft has announced broad pricing changes to Microsoft 365 that take effect July 1, 2026. That might sound far …







.jpg?length=700&name=m365-pricing-changes%20(1).jpg)